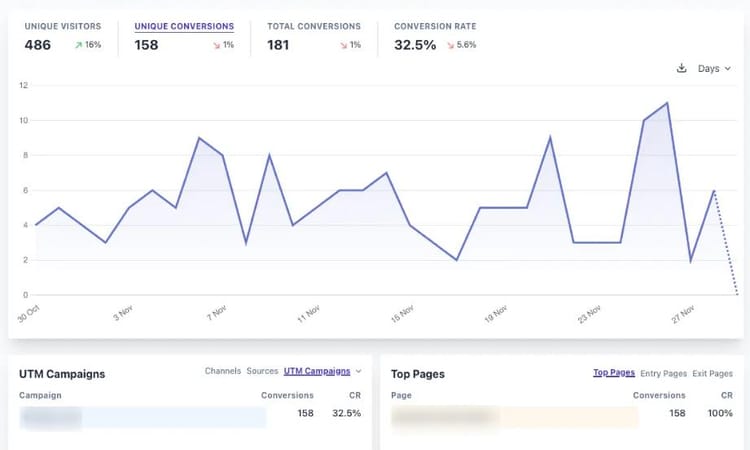
Ditch Google Analytics: Self-hosting Plausible Analytics
Self-host Plausible Analytics in your own cloud – with Docker, reverse proxy, SMTP, GeoIP & auto-updates. A full guide to private, modern tracking — no Google required.
Cloud Sovereignty: Which Providers Meet Our Requirements?
Cloud sovereignty isn't just about location; it's about control, automation, and sustainability. But which providers truly meet business needs? Comparing Hetzner, AWS, Azure, and Google Cloud reveals where your data stays secure and cost-effective.
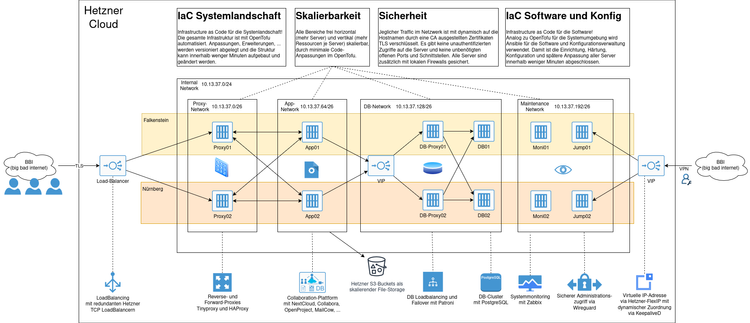
Developing an Autonomous Cloud: In-Depth Insights into Our New Project
Discover how you can achieve true digital independence with open-source software and European service providers. This post explores our journey to building a flexible and secure cloud infrastructure.
Ghost CMS - Table of contents for posts and pages
Ghost CMS lacks a native table of contents (ToC) feature, but with a simple script, you can automatically generate a dynamic ToC for your posts and pages. This guide walks you through the implementation step by step.
Hacked? These Websites Will Tell You If Your Data Has Been Leaked!
Data breaches are increasingly common, exposing sensitive information like emails and passwords. This guide explores trusted services like Have I Been Pwned, Dehashed, and Firefox Monitor to check if your data has been compromised and provides steps to secure your accounts.
The Evolution of Password Security: New Technologies, Trends, and Best Practices
Password security is evolving as weak credentials remain a major risk. This article explores emerging technologies like passkeys, the rise of multi-factor authentication, AI-driven protections, and best practices to safeguard your accounts.
More Than Just Passwords: Features, Risks, and Security Tips for Password Managers
Password managers enhance security by generating, storing, and managing strong passwords. This article explores their benefits, key features, and how to choose the right one.
Digital Education: Safely Navigating a Connected World
In today's digital age, early education on safe internet practices is crucial. This article emphasizes the importance of teaching children about online safety, digital literacy, and responsible behavior to help them navigate the connected world securely.
From Learner to Top of the Class
Recognized as the top IT developer in Berlin, this journey reflects years of dedication, balancing work, family, and intensive study—an inspiration for lifelong learning.